Trends, News, Guides, and Our Expertise
Insights and expert knowledge on Digital Transformation, Risk Management, Information Security, and Regulatory Compliance
Generative AI in the enterprise: From pilot to production-scale rollout
How to take generative AI from pilot to production-scale rollout: the three deployment patterns, five proven use-case archetypes, the compliance layer aligned with EU AI Act and OWASP LLM Top 10 (2025), realistic cost math, and the operating model most pilots never build.
Boris Friedrich
April 24, 2026
Building an AI roadmap: The 4-phase method for enterprise AI transformation
Build an AI roadmap in four phases: potential assessment, use-case selection, pilot, scale. With a 12-18 month timeline, scoring matrix, pitfall taxonomy, EU AI Act and ISO 42001 embedding, and an executive FAQ.
Boris Friedrich
April 24, 2026
What are the 4 Types of AI? The Complete Guide
The 4 types of AI per Arend Hintze (2016): Reactive Machines, Limited Memory, Theory of Mind, and Self-Aware AI. With examples, EU AI Act mapping and what this means for today's enterprise AI use.
Boris Friedrich
April 24, 2026
How to Choose the Right AI Consulting Firm: 10 Criteria for Enterprises
Picking the wrong AI consulting firm costs months and mid-six-figure budgets. This buyer guide scores providers on 10 criteria — regulatory fluency, methodology, MLOps, pricing, data protection — plus an RFP playbook, red flags and the build-vs-buy decision matrix.
Boris Friedrich
April 24, 2026
How to Become an AI Consultant: Career Path, Skills, Certifications 2026
AI consultants translate between business problems and AI engineering. This guide covers the typical 5-7 year career path, ten core skills, the certifications that matter in 2026, and salary ranges across the UK, EU and US — with a clear focus on EU AI Act, ISO 42001 and DORA.
Boris Friedrich
April 24, 2026
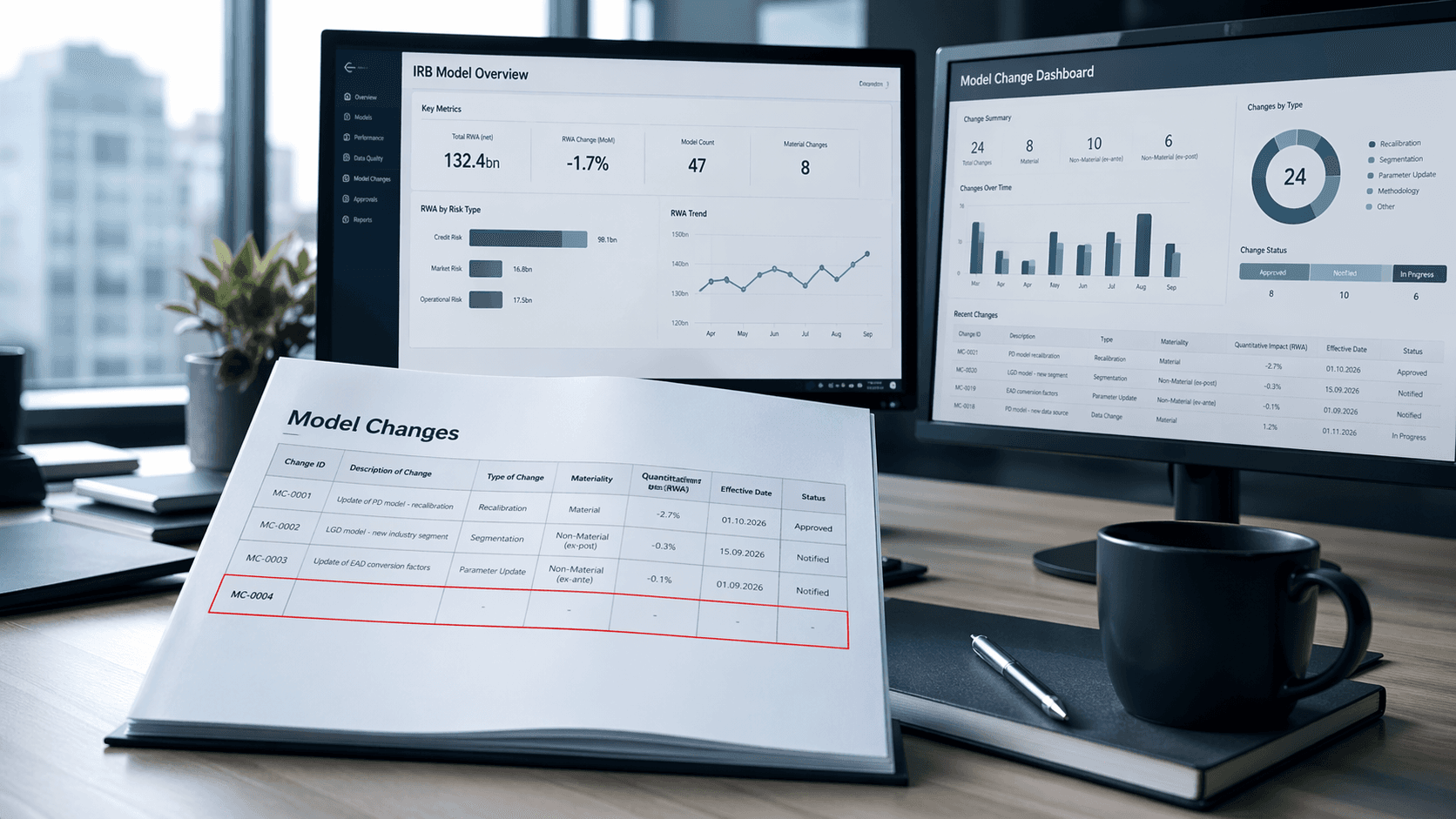
Less & Faster IRB Model Changes — What Actually Changed (and Why It Matters)
How the new IRB rules transform many previously time-consuming model changes into simple notifications—thereby drastically shortening approval times and significantly accelerating implementation
Dr. Helge Thiele
April 24, 2026
Data Governance Framework: Structure, Roles, and Best Practices for Enterprise Data Quality
Data governance ensures enterprise data is consistent, trustworthy, and compliant. This guide covers framework design, the 5 pillars, roles (Data Owner, Steward, CDO), BCBS 239 alignment, implementation steps, and tools for building sustainable data quality.
Boris Friedrich
April 22, 2026
ESG Dashboard: Structure, KPIs & Tools for CSRD Sustainability Reporting
An ESG dashboard makes sustainability performance visible and auditable. This guide covers essential environmental, social, and governance KPIs, CSRD/ESRS alignment, data collection strategies, and tool selection for organizations building audit-ready ESG reporting.
Boris Friedrich
April 20, 2026
Cyber Insurance: Requirements, Costs, and Selection Guide for Businesses 2026
Cyber insurance covers financial losses from cyberattacks, data breaches, and IT outages. This guide explains what insurers require in 2026, coverage types, costs by company size, and how to choose the right policy — including how ISO 27001 certification reduces premiums.
Boris Friedrich
April 17, 2026
Vulnerability Management: The Complete Lifecycle for Finding, Prioritizing, and Remediating Weaknesses
Over 30,000 CVEs are published annually. Effective vulnerability management prioritizes what matters most to your organization and remediates before attackers exploit. This guide covers the full lifecycle: discovery, scanning, risk-based prioritization, remediation, and compliance.
Boris Friedrich
April 16, 2026
DORA ICT Risk Management: Requirements and Implementation Guide for Financial Institutions
DORA Articles 5–15 establish the ICT risk management framework that financial institutions must implement. This guide breaks down governance, framework structure, ICT systems management, detection, business continuity, and the learning loop — with a practical implementation roadmap.
Boris Friedrich
April 16, 2026
Security Awareness Training: Building Effective Programs and Measuring Impact
The human layer remains the weakest link in cybersecurity. This guide covers how to build an effective security awareness program, run phishing simulations, design role-based training, and measure whether your program actually reduces risk — with benchmarks and KPIs.
Boris Friedrich
April 15, 2026
Your strategic success starts here
Our clients trust our expertise in digital transformation, compliance, and risk management
Ready for the next step?
Schedule a strategic consultation with our experts now
30 Minutes • Non-binding • Immediately available
For optimal preparation of your strategy session:
Prefer direct contact?
Direct hotline for decision-makers
Strategic inquiries via email
Detailed Project Inquiry
For complex inquiries or if you want to provide specific information in advance